
In my latest illustration, I depict every day people, minding their own business on the streets, while there are cameras at every corner spying on the masses.
————————————————————-
While the global economy faces potential unemployment and contraction not seen since the Great Depression, the tech giants — and a handful of medium-size ones — are already benefiting from new consumer habits initiated during the lockdowns that analysts believe will turn into longer-term shifts in how people shop, work and entertain themselves. The broader stock markets tanked in recent weeks, but share prices of Amazon and Microsoft hit at or near records. Facebook is moving to acquire high-skilled talent, announcing the hiring of 10,000 new workers this year.
The tech giants‘ deep pockets will enable them to withstand the coming global economic recession, a stark contrast to what industry insiders and analysts expect to be the biggest shake-up of the tech landscape in years. As many start-ups collapse, tech giants will expand on the power they’ve accumulated using the playbook of the last decade: snapping up talent, buying or copying rivals, and eroding traditional industries. Some of those weakened companies may disappear altogether and cede even more territory to tech. Here we explore some of the fast-growing tech players seeking to protect the trust of consumers, and not to mention regulatory obligations, as they continue to fight against the uncertainty of the pandemic’s development.
TikTok, taking over video and also search, by storm
Baidu remains China’s top search engine, with a market share exceeding 70%, according to Forward Industry Research Institute, a Chinese research specialist.
However, ByteDance, best known for its TikTok video-sharing app, has a search engine of its own and is challenging Baidu’s dominance. ByteDance launched its new business by taking advantage of the search function that is integrated into its Toutiao news app. The company has not disclosed how its search engine works. But, said an executive at a Chinese advertising agency: “Its selling point is that results are not affected by the amount of ad fees advertisers pay. And it’s clear the company sees Baidu as its key rival.”
One Guangzhou office worker who recently began using the ByteDance search engine praised it, saying: “Search results that seem to be ads or ad-like are less than half” the number of Baidu’s.
“The excessive amount of ads on Baidu is undermining user convenience,” said Liang Zhenpeng, an IT industry analyst. “Other search engine operators still have an opportunity to enter the market.”
Google, which commands a 90% share of the global search market, has also alienated some of its users. The U.S. company can determine roughly where users are, based on the IP address of their devices, and makes educated guesses about users’ preferences and interests based on their search history. It then uses this data to tailor the results it shows.
While these functions appeal to advertisers, some users find the targeted results off-putting. Critics say Google tends to narrow the scope of results as users perform multiple searches, thereby limiting the search engine’s role as a provider of varied choices.
The number of searches performed on Google fell 8% on the year in the three months to June, while the comparable figure for DuckDuckGo, a rapidly growing search engine developed in the U.S., rose 49% over the same period, according to data marketing company Merkle.
An IT engineer in his 30s in Tokyo has recently begun trying out search engines other than Google. “I don’t like it when I feel that someone is reading my thoughts ahead of time,” he said. The engineer’s favorite search engine is now DuckDuckGo.
“We don’t track you,” is the company’s credo. The search engine is popular because it displays results based solely on the search terms entered. Previous searches have no effect on what shows up in subsequent searches. Gabriel Weinberg, DuckDuckGo’s founder and CEO, believes too much tweaking of search results produces biased thinking.
In addition, more young people are abandoning search engines altogether. Instead, they find what they need using other tools. For example, when searching for restaurants, many internet surfers now look at review sites or use specialized apps instead.
Baidu and Google have spent years establishing seemingly unassailable dominance in search. Earlier in April, Google and Apple announced that they would suspend their rivalry to work with nations of the world to create a new alert system. They would reconfigure their mobile operating systems, incompatible by design, to notify users if they have stepped within the radius of a device held by a COVID‑19 patient.
But the balance of power appears to be shifting.
Another driver of this change is voice search. Smart speakers, car navigation systems, smartphones and other gadgets have voice-recognition capabilities that enable easy-to-use, hands-free search. This will bring information technology ever deeper into people’s lives. U.S. research company Gartner predicts that by next year, 30% of all searches will be done through interfaces that do not require a screen.
This will likely change the way search engines work. Until now, users have mostly typed in search terms and selected from a list of results on a screen. But with smart speakers or other hands-free interfaces, results are also given verbally. That means the search algorithm must select the most relevant options. It will also require different sorts of algorithms than those currently used by search engines.
The Clout that Signal brings to the Chatroom
It’s hard to remember what life was like before modern messaging apps came onto the scene a little over a decade ago. Since their rise alongside the smartphone, they’ve quickly become a primary way people communicate with friends and family. It’s no surprise that such apps usually hold the crown of the most popular apps on Apple’s App Store and the Google Play store.
And messaging apps are big business. The world’s top two messaging apps have over a quarter of the people on the planet using them. WhatsApp has 1.5 billion users worldwide, and Facebook Messenger comes in a close second at 1.3 billion users worldwide, reports Inc. Both of those apps are owned by Facebook. But there are other insanely popular messaging apps used by hundreds of millions or even billions of people on a daily basis, with regional favorites such as China’s WeChat, Korea’s Viber, and Japan’s Line.
The thing about these lists of top messaging apps is that there’s always one notable absence: Signal is never on them. And that’s a shame, because Signal is the most secure, privacy-centric messaging app ever made.
Time and time again it’s been shown that it’s dangerous to trust Facebook with our data. Yet, well over a billion people choose to send their most intimate messages over apps made by the company. And while Facebook says it can’t access messages sent over WhatsApp and doesn’t have access to messages sent via Facebook Messenger, the company does mine your usage of those apps for other data, like how often you talk to someone and whose phone numbers you have stored in your smartphone’s address book.
Facebook doesn’t allow outside privacy and security researchers to inspect its data collection processes, nor the code of its messaging apps. That means we just need to take the company at its word that it’s being responsible with our communications. And studies show that many people are unwilling to make that leap of faith.
So why are people jumping ship from Facebook Messenger and WhatsApp to Signal and not some other messaging platform? Mainly that it is cross-platform friendly and does not mine one’s data for ad targeting. Because Signal is the only major messenger that runs on multiple platforms (iOS, Android, desktop) and steers clear of tracking you and your connections to other people. All the other cross-platform apps track you. And while Apple’s Messages doesn’t, it’s only available on iOS and MacOS devices. Android and Windows users are out of luck.
As you may have heard, Edward Snowden uses Signal. That fact alone usually makes people realize just how secure the app is. All messages are end-to-end encrypted. “But so what?” you might say. Other messaging apps use encryption.
And you’re right: some do. But others don’t. The major messaging apps that use encryption are Apple’s Messages and Facebook’s WhatsApp (which is built on Signal’s encryption, though Facebook mines other metadata about its users). However, Facebook Messenger does not encrypt its messages by default, nor do messaging apps made by Google, such as its Hangouts app.
But Signal does more than just encrypt your messages. It also hides virtually all of the metadata, including who sent the message. That means only the person who the message is being sent to can see who sent it to them. Signal has no way of telling who is sending you other Signal messages, nor does anyone else who intercepts a Signal message in transit. This is pretty much the most security you could ask for in a messaging app. And only Signal offers it.
The likelihood is most of us aren’t and never will be spies or whistle-blowers. But that doesn’t mean we shouldn’t be using the most secure messaging app possible. Even the U.S. Senate urges members and their aides to use Signal. Given that we live in an age where tech giants and data firms have built an entire industry off of mining our data, most of the time without our knowledge and with little regard to the security of that data, why wouldn’t we want to keep our most private, personal, and sensitive communications from them?
But perhaps the best reason to use Signal is that it’s open-source software. This means that anyone in the world can take a peek at its code and verify that the app is as secure as its makers claim. No other major messaging apps would ever dream of allowing that.
————————————————————-
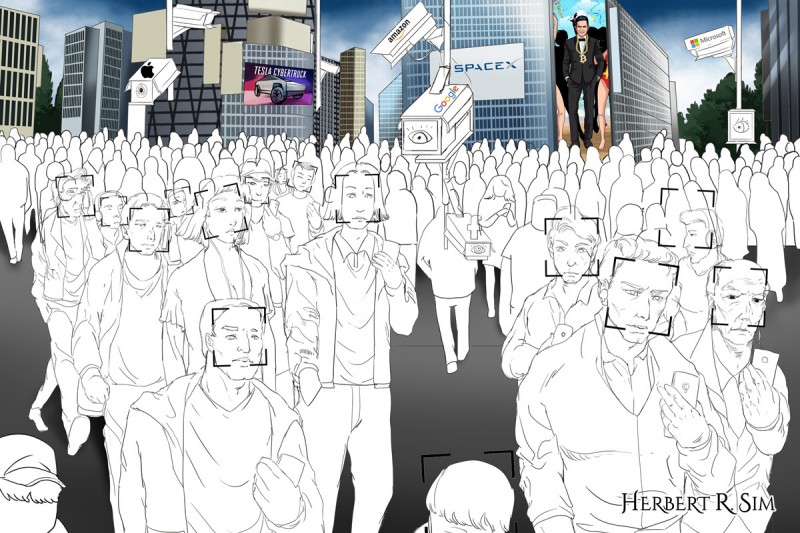
A behind-the-scenes, work-in-progress, coloring in of the illustration sketch.
————————————————————-
Reshaped Regulations In Lieu of the Pandemic
Facebook is indeed busy shaping regulation to its advantage. Last year, it spent roughly $17 million on lobbying—more than any other tech company.
This same basic logic led Amazon to plant its second headquarters on the Potomac River, and it’s led companies like Google and Microsoft to build relationships with the intelligence community. Eminences from these companies sit on official boards that counsel the government about how to upgrade its computing prowess. It’s telling that the nastiest internecine fight among the tech firms involves a $10 billion cloud-computing contract with the Department of Defense.
As the pandemic accelerates Big Tech’s insinuation into government affairs, the industry’s most powerful companies will almost certainly exploit their relationships with agencies to damage less powerful rivals and extract lucrative contracts. But the companies will also provide valuable information and services to their Washington clients, which attracts many of American tech’s biggest solution providers, increasing the government’s powers, for good and for ill.
Shared experience — the name of the game in social media
The rules of social media are evolving quicker than how platforms can update themselves. Private or public forums where participating in a shared experience — often around a specific shared interest — with a like-minded community is the primary purpose for gathering. This looks to be a recurring global practice even as lockdown phases are lifted across countries.
Perhaps the best example of this type of campfire is Fortnite, a multiplayer video game that has more than 200 million users, up to 8 million of whom are online at any given time. The game has been called a de facto social network thanks to the role it occupies in the lives of its players: Indeed, half of teens say they use it to keep up with their friends — some of whom they’ve never actually met in person — with most spending six to 10 hours each week on the platform). Last year, the EDM artist Marshmello staged a virtual concert inside the game that 10.7 million people “attended.” Fortnite is a form of entertainment, but more than that, it’s a catalyst for bringing together like-minded people for a shared experience. And the game’s steep learning curve lends it an aura of exclusivity.
The live broadcasting and viewing platform Twitch serves a similar function. Live streamers, primarily gamers, broadcast their own gameplay, usually with audio commentary, for fans who can watch and interact via chat. Twitch users consumed 592 billion minutes of live-stream content last year, and Twitch has recently pushed into non-gaming categories like music and sports. As with Fortnite, the primary draw to Twitch is its entertainment value, but the “stickiness” comes from the community and sense of excitement that forms around a shared interest or individual.
So how can marketers zero in on the right shared experience campfires for their audience? As with the other campfires, they must first identify the communities and parts of the culture that their brand fits into. Then, determine the online experiences these audiences seek. Brands like the NFL, Marvel, and Nike have done just that, leveraging Fortnite, for example, to reach their audiences by selling skins (stylized weapons and outfits for players’ in-game avatars), creating branded mash-up game modes, and doing limited-edition product drops inside the game.
Without question, the digital campfire trend is firmly on the radar of the big social platforms. “Today we already see that private messaging, ephemeral stories, and small groups are by far the fastest growing areas of online communication,” Mark Zuckerberg wrote in a March 2019 public post, announcing a strategic shift toward more closed, private modes of communication.
Zuckerberg is paying attention to this shift not only because the data shows that Facebook is losing young audiences, but because the re-direction of attention to more private modes of communication represents a major challenge for the company. About 98% of Facebook’s revenue comes from advertising, and people in smaller, more closed forums are much harder for advertisers to reach at scale.
It is neither simple nor straightforward to reach audiences gathered around digital campfires. But as traditional social platforms grow, they become more crowded, and it becomes more difficult and expensive to reach people there anyway. In light of this, digital campfires become a much more attractive alternative — one that requires more groundwork and more careful tending, but one that could potentially have big payoffs for brands in terms of loyalty, retention, and long-term love.
Biometric Data captured by Chinese apps, WeChat Pay and Ali Pay
Mass surveillance is nothing new for China. The country’s use of biometric data is well-regarded as one of, if not the, world’s most invasive. The developing Social Credit System (SCS) has also drawn raised eyebrows for its potential human rights abuses, although its deployment does not yet actually resemble an Orwellian dystopia (and some might argue that the U.S. also has its own form of a social credit system).
On a micro scale, Chinese citizens are used to strict government oversight on their identities. For one, the hukou (household registry) serves as a mechanism for the police to track people’s movements; Chinese citizens are mandated to register with the local police station every time they change residences. Furthermore, pseudonymity is difficult on the Chinese Internet. China has a strong digital identity system, because the government has been promoting a real-name registration system for online activities, particularly for online payments. This means that Chinese citizens must often register for online services with their resident identity card, China’s main identity document, thereby establishing a strong link between real-world identity and online activities.
WeChat Pay and Alipay serve as obvious case studies. As online payment providers, they are subject to KYC, which may run the gamut of identity document verification, biometric matching (i.e. liveness detection), SMS verification, and the provision of further details, like bank card / bank account details. Together, they have about 92.7 percent market share of the Chinese payment market, which boasts an 86 percent penetration rate of the Chinese population. Since they are also part of a sprawling ecosystem of products and services of their parent companies—Tencent and Alibaba, respectively— that includes food delivery apps, ecommerce sites, gaming, entertainment, and more. Tencent and Alibaba have the potential to collect a massive amount of user details, all linked to any individual’s real-world identity. Projects like WeChat’s pilot programs for digital identity cards only stand to reinforce an already solid link between real identity and one’s digital identity.
And even if apps and services do not require or use extensive identity verification protocols, the mobile phone number is often required for use of services, such as social media platforms. The phone number in itself is a strong link to one’s real identity, because users must register for SIM cards with their identity cards or passports and must submit to facial recognition scans. While the government’s use of digital identity is not well-advertised for obvious reasons, censorship on social media platforms and even private chats is a good starting point for understanding the insidious effects of a persuasive identity schema that lives no room for (pseudo)-anonymity, not even on the Internet. In seconds, technology can recognise a politically-sensitive post or text—and then identify the culprit with high assurance.
Asia Takes Over e-Commerce With Surveillance Capabilities
E-commerce has experienced unprecedented growth over the last two decades. While much of that has occurred in developed markets with wide internet access, there is still a lot of untapped growth potential for the industry in emerging markets.
According to a report by Business Times Singapore, fashion e-commerce firm Zilingo employs a team of “white hat hackers” – also known as ethical hackers – every three to six months to uncover vulnerabilities in the company’s systems. The company’s chief technology officer Dhruv Kapoor says that of the over 100 employees at Zilingo, about a tenth looks either exclusively or partially at security.
It’s in the culture as well, he says. “Our company culture requires us to think about privacy and security from the very start, when there is a new product idea or the start of a business plan.”
For instance, Zilingo recently launched a service that would allow merchants to check on the progress of an order placed at a factory – but not before working with partners to create a framework where factories’ data is securely shared in a way that does not compromise privacy.
The truth is, e-commerce startups – and Big Tech firms – exist in a world where bad actors are becoming more sophisticated. For example, depending on how a machine learning model was constructed, it is possible for an adversary to “reverse engineer” the model and uncover the underlying data on which it was based.
In a New York Times report, Justin Zeefe, a former intelligence officer who is now the president of Nisos, a security firm in Virginia, said his company has worked for tech companies on a wide range of cases. On one occasion, they learned that a company’s overseas suppliers had ties to foreign intelligence agencies.
Another client asked his firm to determine whether an acquisition target had been infiltrated by foreign hackers. Yet another hired Nisos to determine the source of multiple cyber-attacks. It turned out to be the work of a competitor that had intercepted the company’s Wi-Fi from an apartment rented across the street.
Third-party service behavior is constantly changing, and most third-party vendors bring in a fourth party, which has no contractual agreement or visibility into the native brand. These fourth-party services have the same level of data access, but operate without the oversight or even the knowledge of the retailer that they’re operating, collecting and transferring customer data on their sites, posing a substantial risk to consumer privacy.
This lack of visibility and understanding around these blind spots is the cause of many high-profile data breaches. While most sites have privacy measures in place, sensitive customer data is still being collected by outside parties, putting the native site at risk of a major data breach. With 63 percent of data breaches linked directly or indirectly to third-party access according to Total Retail, retailers will have to find a balance between creating seamless experiences and consumers’ privacy.
Why The Data Revolution Requires a Greater Tech Reckoning
Companies such as Apple, Experian, and Google, which have promised to develop tech tools to battle Covid-19, must also guard against the intense scrutiny of their data collection and user tracking practices, from lawmakers and, especially in the U.S., from the wary public.
Protecting the trust of consumers, and not to mention regulatory obligations, have caused tech companies to cautiously contribute to the pandemic fight.
As tech giants like Apple, Experian and Google continue battling the pandemic with digital tools, more innovation should come into play for the nimbler, smaller players.
This crisis will eventually pass and, as new data challenges arise, privacy technologies must become the standard for enterprises and governments alike, to ensure we are best equipped to facilitate wide-scale privacy-enabled data collaboration before the next crisis unfolds.
————————————————————-

In my final illustration in full color, the brands featured include: Apple, Amazon, Google, Facebook, Netflix, Microsoft, Tesla, SpaceX, and of course, Tik Tok.
————————————————————-
Setting The Stage For Data Privacy
Overall, the privacy market has improved, press attention is steady, the number of privacy-related stories is increasing across all channels, and the recent wave of high-level fines and warnings of intent against Facebook ($5 billion), British Airways (£183 million) and Marriot (£99.2 million) certainly caught the eye.
According to the IAPP in an interview with companies from different segments, budget is still a problem. Privacy has taken center stage in recent months and the focus on compliance has increased, but this was not reflected immediately in companies’ budgets.
The challenge of selling a privacy program to senior management is that the benefits are not yet widely understood and there are no tangible benefits. You cannot see it, you cannot touch it, and it is very difficult to demonstrate a return on investment, unless there is a breach or there are violations and sanctions applied to similar companies or a direct competitor that would lead the board of directors to question: “What if it happens to us?”
Creating an effective privacy framework requires cultural change. A change that takes time and offers benefits that are not always immediately visible, but many companies and, in fact, shareholders are not patient and expect immediate results.
Investing in technology for privacy (PrivacyTech) costs money. For an organization to spend money, there must be a benefit, and for many, the benefits are not yet tangible. This change, which is seeing privacy as an asset, requires a change in the corporate mindset. Privacy and data protection as a whole needs to be seen as a competitive differentiator, not a burden and when this happens in the emerging markets as it has already been happening in the rest of the world, PrivacyTech will be expanding and in strategic positions in all sectors of the economy, including the other “techs.”
Users generate data and companies profit enormously from it, so users should have some stake or incentive in it. Chris Hughes, Facebook co-founder and author of the bestseller ‘Fair Shot: Rethinking Inequality and How we Earn’, is a proponent of the idea that since companies profit from the data pooled in by multitude of users, the economic dividends should accrue to the users as well, and not just remain in the coffers of a handful few businesses. He cites the Alaskan Permanent Fund, wherein all citizens of Alaska are given a dividend by the oil companies that explore oil in Alaska. While this approach may sound a bit too radical, it is just one of the many approaches that focus on users being at the core of the data business and thus entitled to have a say in the way their data is being used, or receive a share in profit.
The Neo-Liberal economic consensus is being shattered and leading business tycoons are more than vocal in calling for reimagining capitalism and shifting the focus from shareholders to more inclusive stakeholders. Data business, which is at the core of tech innovations and disruptive paradigms of the future, cannot function the way it hitherto has.
Another interesting approach that companies are getting interested in is ‘Privacy by Design’, which refers to by-default privacy in a system becoming a prime concern of any enterprise. This is not only ethical but would also boost consumer confidence, which would translate to better brand image and abiding relationship with the customers. Innovation requires transparency, accountability and a conducive environment. All of these are interlinked, with transparency being the first prerequisite for making any system secure and robust. Embedding privacy at the core should be done in such a way that it doesn’t hamper functionality or make the system or app counterproductive. ‘Privacy by design’ is a proactive approach that will preempt privacy breach. It also improves the functionality of a system and enhances accountability, openness and compliance.
Ed Parsons, Geospatial Technologist, Google, sums it up perfectly: “Data privacy is largely about transparency and education. It’s about making it clear when information is gathered about an individual, what that information is going to be used for, and giving control to that individual about whether that information is used or not.”
